The Wireshark Challenge: how to ensure the security of open-source projects with formal methods? - TrustInSoft, exhaustive static analysis tools for software security and safety
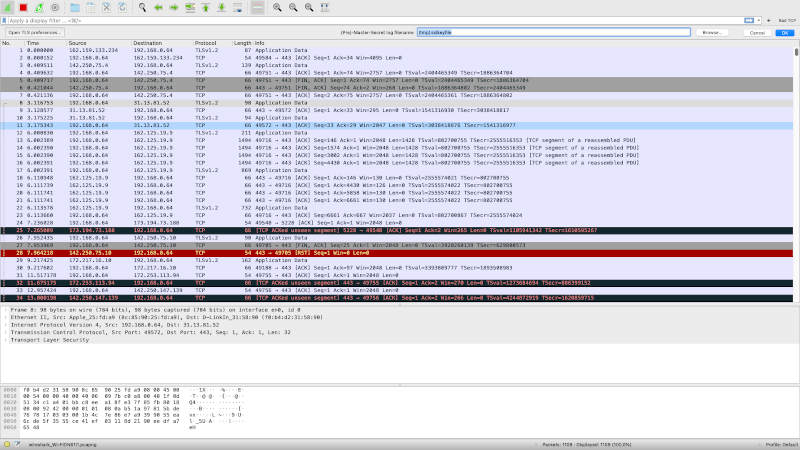
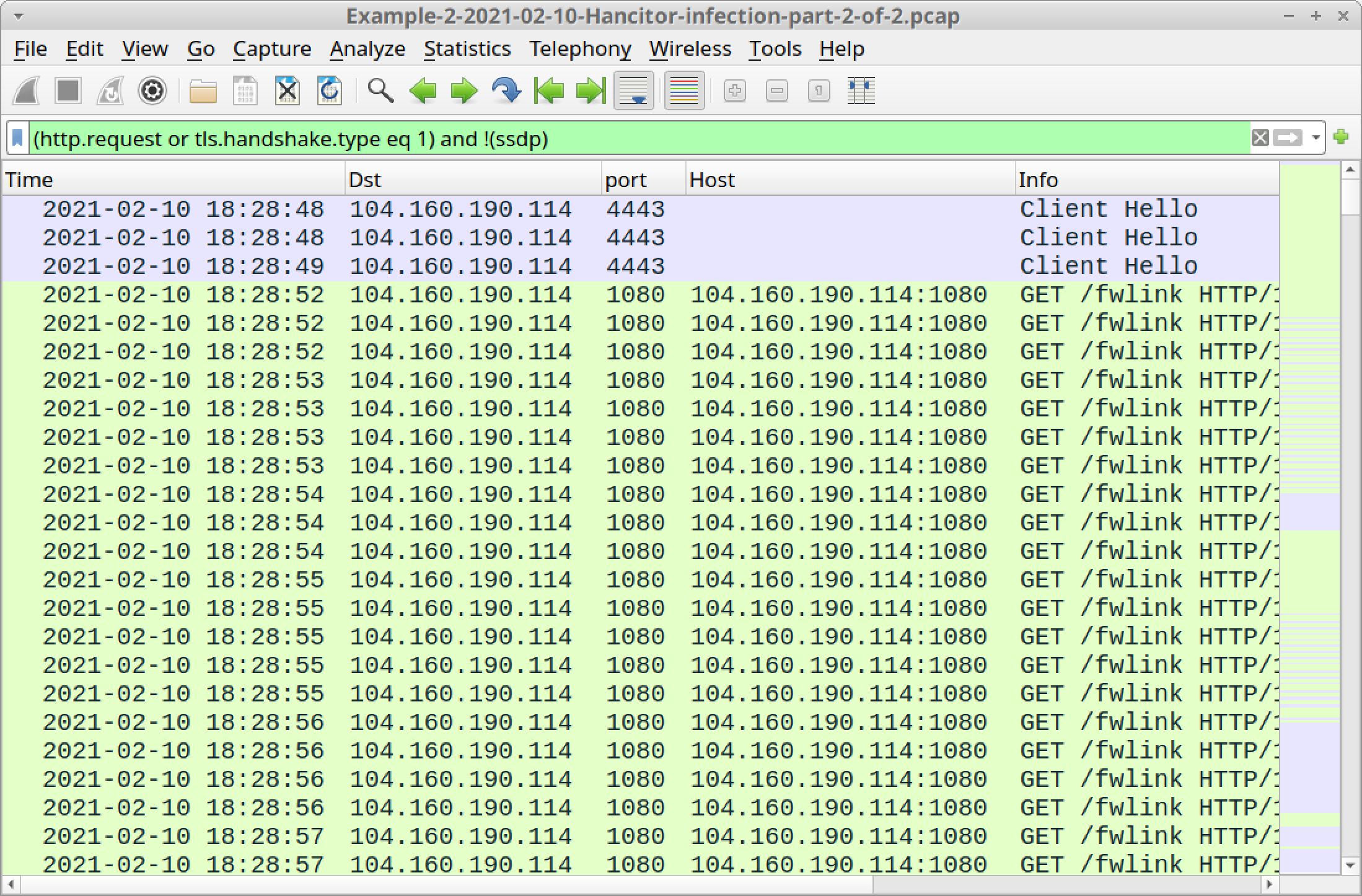
Screenshot of a Wireshark capture of a communication between the client... | Download Scientific Diagram

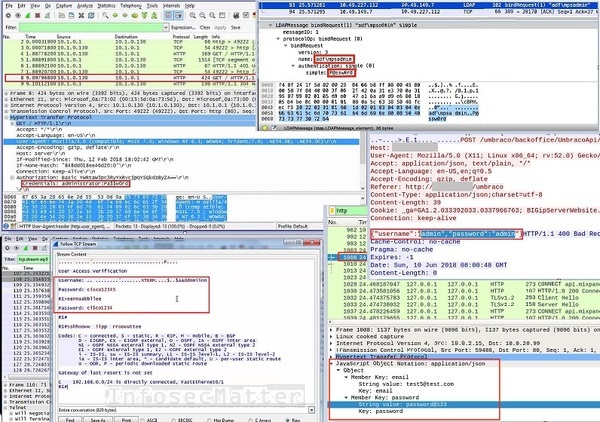
![How to Use Wireshark Network Protocol Analyzer [Full Tutorial] How to Use Wireshark Network Protocol Analyzer [Full Tutorial]](https://cdn.comparitech.com/wp-content/uploads/2018/12/How-to-Use-Wireshark-tutorial.jpg)